Using fb://webview deep link it is possible to bypass linkshim protection and user redirected to evilzon site without notice.
Continue reading “Facebook: Linkshim protection bypass using fb://webview”Perform substring search for emails even if Workplace admin hides email profile field.
Description:
Attack can perform substring search for emails even if Workplace admin hides email profile field.
As admin From the Admin Panel, goto Settings >> Profile fields >> on Email field Turn visibility off.
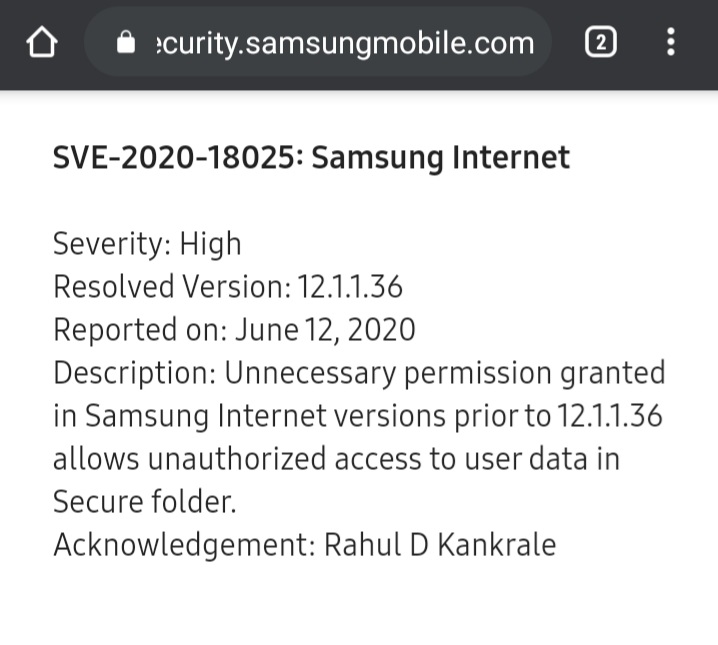
Continue reading “Perform substring search for emails even if Workplace admin hides email profile field.”Bypass Samsung Knox protection to read files stored in a secure folder | Android
Description: Samsung Knox is a defensive mobile security platform that is built into Samsung devices and enhances security in all directions through a combination of physical means and software systems, providing security protection from the hardware to the application layer.
I used the path and file structure to bypass Samsung Knox protection in an unauthorized manner to read the stored files in the secure folder, and received a Samsung $3750 reward.
Severity: High | SVE-2020-18025
Continue reading “Bypass Samsung Knox protection to read files stored in a secure folder | Android”Xiaomi Android : Harvest private/system files (Updated POC)
Yet another android vulnerability which I found on Xiaomi: giant mobile manufacturer company.
Summary: There inbuilt SMS is an application pre-installed on those devices. The application is built with feature which sync in to cloud using webview through application’s sandbox.
This application can also be launched from the browser and have its WebView directed to load an arbitrary URL and allow access to local file system, read local resources and access network resources.
Information disclosure through javascript bridge in Android
Summary: One of the top most phone company has info Disclosure vulnerability in there inbuilt sms app.
Continue reading “Information disclosure through javascript bridge in Android”DoS on Facebook Android using 65530 chars of ZERO WIDTH NO-BREAK SPACE.
Summary: It was possible to delete facebook users draft and settings using DoS with zero width no-break space.
Continue reading “DoS on Facebook Android using 65530 chars of ZERO WIDTH NO-BREAK SPACE.”Twitter Android Javascript Interface Vulnerability
Summary: com.twitter.android.lite.TwitterLiteActivity was set to exported, data passed to intent was not validated and its web view has JSInterface that available to any URL which was loaded through this activity as well as insecure schemes like file, javascript was available through intent.
Continue reading “Twitter Android Javascript Interface Vulnerability”From NA to $3000 : Facebook’s URL spoofing vulnerability
Summary: This could have let a malicious user spoof the URL bar of multiple Facebook Android apps by navigating to a different domain on the original tab after a new tab had been opened using the setInterval method.
Continue reading “From NA to $3000 : Facebook’s URL spoofing vulnerability”